Insights & Resources
Discover expert insights, real-world results, and ready-to-use resources that make it easier to protect people, safeguard data and stay compliant.
When the Worst Happens: Why Backups Are Your Last Line of Defence Against Ransomware 
Cyber Security Awareness
When the Worst Happens: Why Backups Are Your Last Line of Defence Against Ransomware
Read more
The Data (Use and Access) Act 2025: What CISOs Need to Know in 2026 
Governance, Risk, Compliance GRC
The Data (Use and Access) Act 2025: What CISOs Need to Know in 2026
Read more
Your AI Agent Doesn’t Need Its Own Desk (But It Does Need Its Own Password) 
Our BlogCyber Security Awareness
Your AI Agent Doesn’t Need Its Own Desk (But It Does Need Its Own Password)
Read more
What “Good” Really Looks Like Under NIS2: Turning Policy into Behaviour Change 
Governance, Risk, Compliance GRCOur Blog
What “Good” Really Looks Like Under NIS2: Turning Policy into Behaviour Change
Read more
The Human Side of Cyber Security Sales: Louise Bohan on Confidence and Career Growth 
Our Blog
The Human Side of Cyber Security Sales: Louise Bohan on Confidence and Career Growth
Read more
Trust Under Threat: How Deepfakes Are Redefining Organisational Risk 
Cyber Security Awareness
Trust Under Threat: How Deepfakes Are Redefining Organisational Risk
Read more
Handing Your Passport to a Stranger: The Obvious Gap in Autonomous AI 
Cyber Security Awareness
Handing Your Passport to a Stranger: The Obvious Gap in Autonomous AI
Read more
NIS2 Compliance Won’t Fail On Technology. It Will Fail On People. 
Our BlogGovernance, Risk, Compliance GRC
NIS2 Compliance Won’t Fail On Technology. It Will Fail On People.
Read more
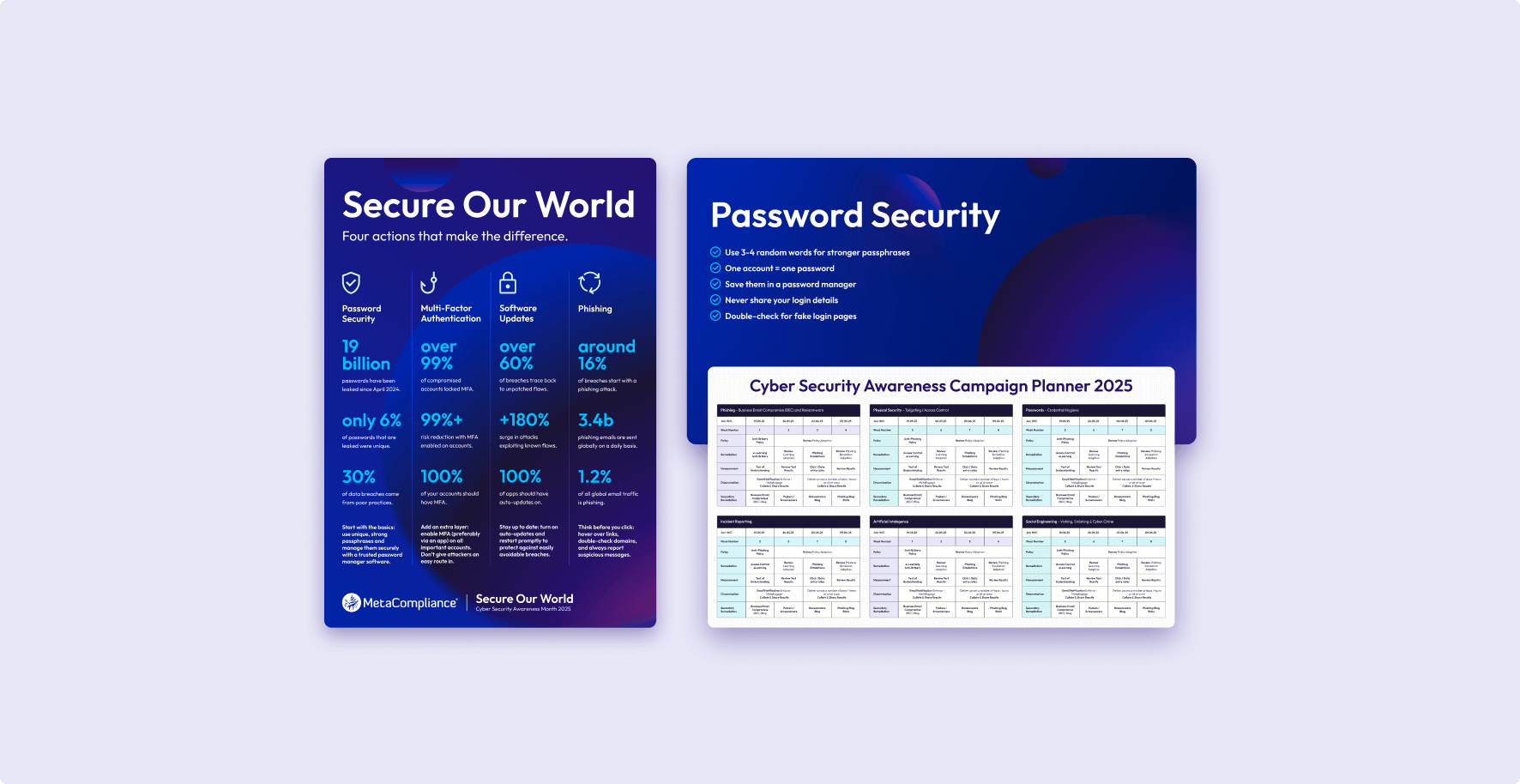
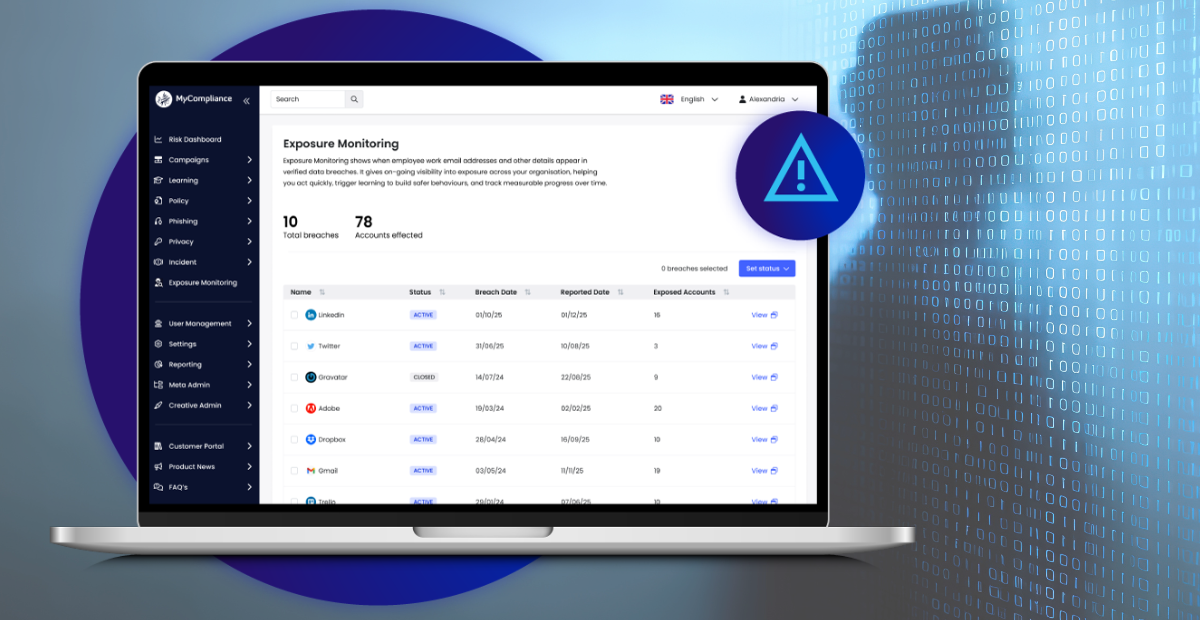
Your Next Step in Cyber Security Awareness
Resources are just the beginning. Partner with MetaCompliance to deliver personalised training that drives compliance, changes behaviour, and reduces risk.