A strong password policy is often the first line of defence against cyber attacks, yet many organisations continue to follow outdated guidelines that expose them to significant risk.
According to Verizon’s 2020 Data Breach Investigations Report, lost or stolen credentials remain the number one hacking tactic used by malicious actors to perpetrate data breaches, with compromised or weak passwords responsible for 35% of all breaches.
Password security has never been more important, especially with large numbers of the workforce continuing to work from home. The threat surface has expanded so it’s crucial that organisations update their password policy to educate staff on how to create strong passwords and provide a robust defence against cyber threats.
Previous guidance on password security tended to focus on uniqueness, complexity, minimum password length, and regular password changes; however, the latest advice has moved away from this as many of these password practices could in fact cause users to create weaker instead of stronger passwords.
The National Institute of Standards and Technology (NIST) has addressed the importance of password policies by issuing NIST Special Publication 800-63B (Digital Identity Guidelines – Authentication and Lifecycle Management). The publication provides up to date advice for organisations on how they can improve the authentication process and reduce the risk of a security breach.
Microsoft and the National Cyber Security Centre (NCSC) have all also updated their guidance on passwords to help organisations implement password policies that can defend against evolving threats and support the ways in which people naturally work.
To ensure your password policy is effective and meets the standards recommended by NIST, Microsoft, and the NCSC, we’ve compiled all the latest guidelines into actionable advice that your organisation can use to improve password security.
Password Policy Best Practices
Increase password length and reduce the focus on password complexity
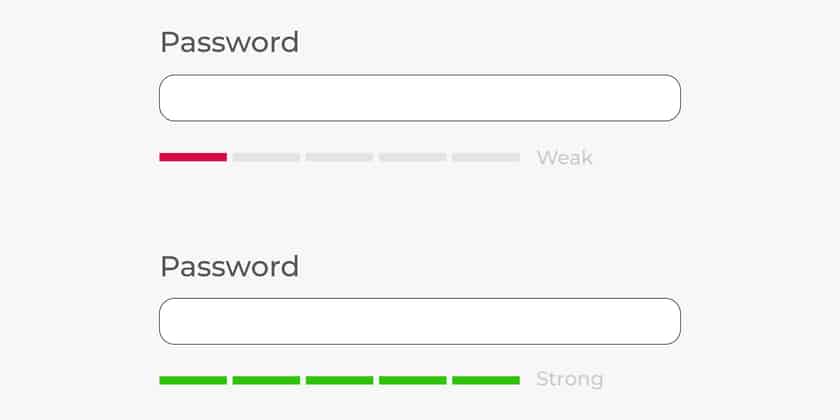
In the past, advice on password security has focused heavily on the creation of complex passwords, but this often leads to the reuse of existing passwords with minor modifications. According to the National Cyber Security Council: “Complexity requirements place an extra burden on users, many of whom will use predictable patterns (such as replacing the letter ‘o’ with a zero or using special characters) to meet the required ‘complexity’ criteria.
Attackers are familiar with these strategies and use this knowledge to optimise their attacks.” Password length is often a much more important factor as a longer password is statistically more difficult to crack. NIST and Microsoft advise a minimum length of 8 characters for a user-generated password, and to bolster security for more sensitive accounts, NIST recommends organisations set the maximum password length at 64 characters. This allows for the use of passphrases. A passphrase is a password composed of a sentence or combination of words. It helps users memorise longer passwords and makes it more difficult for hackers to guess using brute force.
Screen passwords against blacklists
Password reuse is a common problem and according to a Google/Harris survey, 52% of people reuse the same password across multiple accounts. This risky behaviour has led to a huge surge in credential stuffing attacks as hackers attempt to cash-in on the billions of compromised credentials available to buy on the dark web. Using these stolen credentials, hackers can attempt to access additional user accounts using the same compromised password.
To combat this threat, NIST recommends that organisations utilise software that screens passwords against a blacklist that includes dictionary words, repetitive or sequential strings, passwords stolen in previous breaches, commonly used passphrases, or other words and patterns that hackers could guess. This screening process helps users avoid selecting passwords that pose a risk to security and will flag up if a previously safe password becomes exposed in the future.
Eliminate regular password resets

Many organisations require their employees to change their passwords at regular intervals, often every 30, 60 or 90 days. However, recent studies have shown that this approach to password security is often counter productive and can in fact make security worse. Typically, users will have multiple passwords that they need to remember, so when they are forced to do a periodic reset, they will resort to predictable behavioural patterns such as choosing a new password that is only a minor variation of the old one.
They may update it by changing a single character or adding a symbol that looks like a letter (Such as ! instead of I). If an attacker already knows the user’s existing password, it won’t be too hard to crack the updated version. NIST recommends removing this requirement to make password security more user-friendly, and Microsoft advises: “If a password is never stolen, there’s no need to expire it. And if you have evidence that a password has been stolen, you would presumably act immediately rather than wait for expiration to fix the problem.”
Allow password copy and paste
NIST has revised its previous guidance and now recommends the use of ‘copy and paste’ when typing in a password. This helps promote the use of password managers which undoubtedly increases security by enabling users to generate longer passwords which are more difficult to crack.
Limit Password attempts
Using brute-force attack, hackers may attempt to breach an account by systematically logging in and trying every possible combination of letters, numbers, and symbols until they work out the right password combination. One of the best ways to defend against this type of attack is limiting the number of password attempts that any single IP address can make within a certain time frame.
Don’t use password hints
Password hints are frequently used by organisations to help their users remember complex passwords. It may be a simple prompt or the user is required to answer a personal question such as ‘what city were you born in?’ or ‘What is the name of your first school?’. The answers to many of these questions can easily be found on social media by a determined attacker. This undermines security which is why NIST has advised organisations to drop this practice as it could potentially increase the chance of a breach.
Use Multi-Factor Authentication

Multi-factor authentication (MFA) is one of the most effective ways to provide additional protection to a password-protected account. According to Microsoft, accounts are more than 99.9% less likely to be compromised if MFA is enabled. However, a recent GetApp survey found only 55% of respondents use two-factor authentication by default for their business and personal accounts when it is available.
There are three types of authentication that can be used:
- Something you know: A password, PIN, postcode, or answer to a question (ex: mother’s maiden name).
- Something you have: A token, phone, credit card, SIM, or physical security key.
- Something you are: Biometric data such as a fingerprint, voice, or facial recognition.
Some of these verification methods are undoubtedly more secure than others but essentially it means that even if someone steals or guesses a password, they won’t be able to access the account without another authenticating factor.
Train staff on password best practice
There’s lots of conflicting advice on what constitutes a secure password so it’s crucial that your staff understand best practice and are fully versed on what your password policy requires of them. Security awareness training should educate staff on:
- The risks of reusing the same passwords across home and work accounts
- How to create strong and secure passwords
- How to enable MFA
- How to use an automated password manager to store passwords securely








